Lost Keys, Lost Assets: Wallet Recovery Security Becomes a Critical Issue
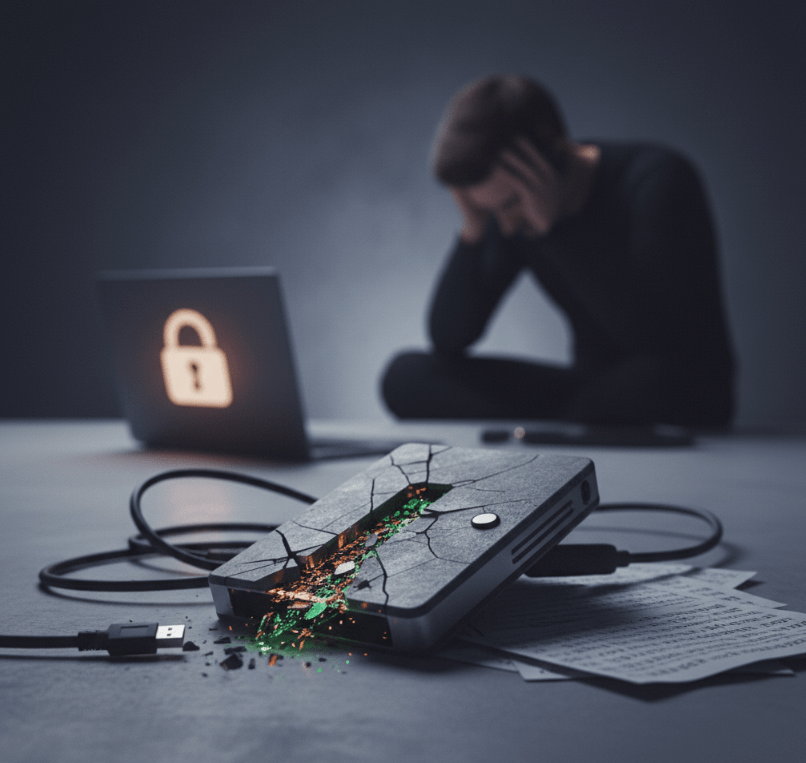
Wallet recovery security has emerged as one of the most underappreciated yet devastating challenges in the crypto ecosystem. As self-custody becomes the preferred method of holding digital assets, millions of users now shoulder full responsibility for safeguarding their private keys and recovery phrases. While this shift aligns with decentralization ideals, it has introduced a harsh reality: if access credentials are lost, assets are gone forever.
Unlike traditional banking systems where identity verification can restore account access, blockchain networks offer no such safety net. Consequently, wallet recovery security has become a defining factor in determining whether self-custody is truly viable for mainstream adoption. As cases of irreversible asset loss continue to surface, the industry faces mounting pressure to improve recovery mechanisms without compromising decentralization.
Seed Phrases: The Single Point of Failure
At the heart of most wallet recovery systems lies the seed phrase, a sequence of words that grants full control over crypto assets. While seed phrases simplify backup processes, they also create a single point of failure. If the phrase is lost, destroyed, or stolen, there is no alternative path to asset recovery.
Many users underestimate this responsibility during initial wallet setup. Some store seed phrases digitally, exposing them to malware or cloud breaches. Others write them down on paper, which can be misplaced, damaged, or discovered by unauthorized individuals. As a result, wallet recovery security incidents often stem from simple human error rather than technical failure.
Irreversible Losses Mount Across the Industry
Blockchain analytics firms estimate that billions of dollars’ worth of cryptocurrency has been lost due to inaccessible wallets. These losses occur when users forget passwords, misplace seed phrases, or pass away without sharing recovery information. Because blockchain networks do not recognize identity, there is no authority capable of reissuing access.
These incidents have real financial and emotional consequences. Families have reported being unable to inherit digital assets, and long-term investors have watched holdings vanish due to forgotten credentials. Such cases highlight how wallet recovery security is not merely a technical concern but a human one with life-changing implications.
Social Engineering Threats Complicate Recovery Security
Beyond accidental loss, seed phrases have become prime targets for social engineering attacks. Scammers impersonate wallet support teams, exchange representatives, or even law enforcement, convincing users to reveal recovery information under false pretenses. Once disclosed, assets can be drained instantly.
The rise of AI-generated impersonation, deepfake voice calls, and highly personalized phishing messages has further intensified this threat. As deception techniques evolve, traditional awareness campaigns struggle to keep pace. Therefore, wallet recovery security increasingly depends on both technological safeguards and continuous user education.
Hardware Wallets Offer Protection but Not Immunity
Hardware wallets are widely regarded as the safest self-custody solution, yet they do not fully solve recovery challenges. If a hardware device is lost or destroyed, the seed phrase remains the only recovery method. Conversely, if a user improperly records the phrase during setup, the hardware wallet’s security becomes irrelevant.
Additionally, counterfeit hardware devices and tampered packaging have led to supply chain scams where attackers preconfigure seed phrases before selling devices to unsuspecting users. These incidents have revealed that wallet recovery security must extend beyond software design into manufacturing, distribution, and retail channels.
Social Recovery Solutions Gain Momentum
To address the harsh consequences of lost seed phrases, wallet developers are experimenting with social recovery systems. These methods allow users to appoint trusted contacts or devices that can collectively restore access if credentials are lost. By distributing recovery authority, social recovery aims to remove the single point of failure inherent in seed phrases.
However, social recovery introduces its own risks. Trusted parties could collude maliciously or become compromised themselves. Developers must therefore balance convenience with security, ensuring that recovery mechanisms cannot be exploited as new attack vectors. Despite these concerns, social recovery is gaining traction as a potential breakthrough in wallet recovery security.
Multi-Signature Wallets Reduce Recovery Risks
Multi-signature wallets represent another approach to improving recovery resilience. Instead of relying on a single private key, these wallets require multiple keys to authorize transactions. This structure allows one key to be stored as a backup or entrusted to a secure third party.
While multi-signature setups improve security, they add complexity that can overwhelm average users. Mismanaging multiple keys can inadvertently recreate the same loss risks they are designed to prevent. As a result, usability remains a major hurdle in making advanced recovery models widely accessible.
Estate Planning Enters the Crypto Conversation
As crypto ownership becomes more widespread, estate planning has emerged as a new dimension of wallet recovery security. Legal professionals are now developing methods to ensure heirs can access digital assets without exposing them to theft during the owner’s lifetime.
These arrangements often involve encrypted backups, legal custodians, or structured inheritance contracts. However, regulatory uncertainty and technical challenges complicate these solutions. Until standardized practices emerge, inheritance-related wallet recovery remains a fragile and often overlooked risk.
Industry Efforts Toward Better User Experience
Recognizing that complexity contributes to user mistakes, wallet providers are investing heavily in improving onboarding and recovery guidance. Interactive setup flows, warning prompts, and educational content are now common features in modern wallet applications.
Some developers are also exploring password-based recovery layers, though these must be carefully designed to avoid reintroducing centralized control or data exposure risks. The goal is to make wallet recovery security robust without making self-custody intimidating for new users.
Regulatory Interest in Consumer Protection
Regulators have begun examining whether wallet providers should bear partial responsibility for recovery-related losses. Discussions include whether minimum recovery standards, disclosure requirements, or consumer protection guarantees should apply to wallet services.
While direct regulation of self-custody remains controversial, the growing scale of irreversible losses has made wallet recovery security a public policy issue. Future regulatory guidance could influence how wallets design recovery features and communicate risks to users.
The Trust Factor in Self-Custody Adoption
Mass adoption of self-custody hinges on whether users feel confident they can recover assets if something goes wrong. As long as wallet recovery remains unforgiving, many potential users may prefer custodial solutions despite their risks.
Therefore, improving wallet recovery security is essential not only for protecting existing users but also for expanding crypto participation. Solutions that combine decentralization with practical recovery safeguards will likely define the next generation of wallet technology.
The Road Ahead for Wallet Recovery Security
Looking forward, wallet recovery security will remain a pivotal challenge in the crypto industry. The tension between absolute control and absolute responsibility is at the heart of self-custody. Bridging this gap requires innovation in cryptography, user experience, and security education.
As new recovery models mature and awareness grows, the industry may eventually overcome one of crypto’s most unforgiving design traits. Until then, the fate of many digital fortunes will continue to depend on how well individuals guard a simple string of words.




